Small Steps to Big Gains
Small Steps to Big Gains
Your guide to PCI security standards and compliance
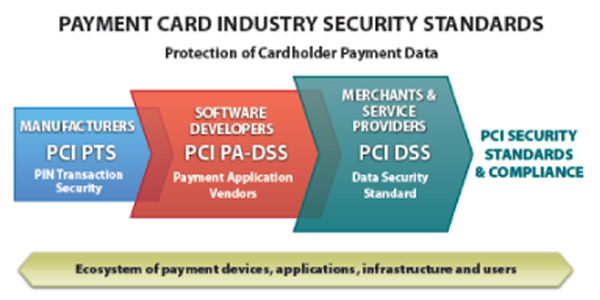
PCI Security Standards
The PCI Data Security Standard (PCI DSS)
- Applies to any entity that stores, processes, and/or transmits cardholder data
- Covers technical and operational system components
The Payment Application Data Security Standards (PA-DSS)
- Applies to developers and integrators of applications involved in authorization or settlement.
- Governs these applications that are sold, distributed or licensed to third parties.
The PIN Transaction Security (PTS)
- Applies to manufacturers of personal identification number (PIN) entry terminals used for payment card financial transactions.
| Goals | PCI DSS Requirements |
| Build and maintain a secure network | 1. Install and maintain a firewall configuration to protect the cardholder data |
| 2. Do not use vendor supplied defaults for system password and other security parameters | |
| Protect cardholder data | 3. Protect stored cardholder data |
| 4. Encrypt transmission of cardholder data across open and public networks | |
| Maintain a vunerability management program | 5. Use and regularly update anti-virus software |
| 6. Develop and maintain secure systems and applications | |
| Implement strong access control measures | 7. Restrict access to cardholder data by business need to know |
| 8. Assign a unique ID to each person with computer access | |
| 9. Restrict physical access to cardholder data | |
| Regularly monitor and test networks | 10. Track and monitor all access to network resources and cardholder data |
| 11. Regularly test security systems and processes | |
| Maintain an information security policy | 12. Maintain a policy that addresses information security for all personnel |
| Type | PCI DSS Designation | Activity |
| Assessment | Internal Security Assessor (ISA) | Merchant resource certified to validate compliance of PCI DSS |
| Qualified Seurity Assessor (QSA) | Independent third party certified to validate compliance of PCI DSS | |
| Payment Application Qualified Security Assessor (PA-QSA) | Independent third party certified to evaluate compliance of Payment Applications to the PA-DSS | |
| Network Scanning | Approved Scanning Vendor (ASV) | Independent third party accredited to perform network vulnerability scan |
| Foresics Investigation | PCI Forensics Investigator (PFI) | Independent third party accredited to perform forensics investigation in the event of suspected cardholder data breach |
| Laboratory | PCI Recognized Laboratory | Independent third party certified to validate compliance of PIN Transaction Security Standards |
| Merchant Level | Volume | Requirements | Compliance Validation Target |
| 4 | Less than 20,000 ecommerce or less than 1 million transactions with one card brand |
|
12/31/2006 |
| 3 | Between 20,000 and 1 million Visa or MasterCard ecommerce transactions in a 12 month period |
|
12 months from date of notification |
| 2 | Between 1 and 6 million Visa or MasterCard transactions in a 12 month period |
|
Dec 31st of year following notification** |
| 1 | Greater than 6 million Visa or MasterCard transactions in a 12 month period |
|
September 30th of year folloing notification** |
(*) MasterCard now requires Level 1 and Level 2 merchant assessments to be performed by as assessor – QSA or ISA
(**) MaterCard requires all Level 1 and Level 2 merchants to validate compliance by June 30, 2011
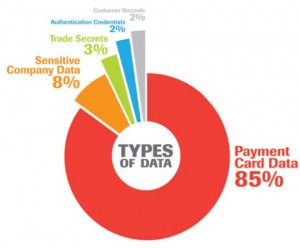
What Do Hackers Want?
Payment Card Data is a target for criminals looking to turn data into cash quickly
How Breaches Happen…
Remote (Internet) attack
- Attacker finds a system, directly connected to the Internet
- Exploits an un-patched vulnerability to take control of the system
- Downloads cardholder data from the payment application
- Installs malware on the system to steal future transactions
Point-of-Sale terminal theft and/or swap
- Attacker steals a terminal
- Extracts existing cardholder data
- Installs a skimmer
- Swaps compromised terminal with new terminal at another location and repeats
Top 5 reasons Breaches Happen:
- #5 – Device Tampering
- #4 – Default Passwords
- #3 – No Anti-Virus protection
- #2 – Known vunerabilities not patched
- #1 – No Firewall
What can you do?
#5 – Payment Hardware Best Practices
- Securely mount terminals to deter theft
- Use pCI PTS validated terminals
- Tamper resistant if stolen
- Memory is deleted if device is opened
- PIN encryption key is deleted if device is opened
- Cannot be used in skimmer/replacement attack
- Required by July 1, 2010 for merchants accepting PIN Debit
- Tamper resistant if stolen
- COST: Varies by terminal
#4 – Use Strong Passwords
- Change the default password on a new system
- Choose a good password
- Easy to remember
- Hard to guess
- Mixed Case, Alpha-Numeric, Special characters
- Pink Floyd
- Pink Floyd!
- P1nk F10yd!
- F10yd!P1nk
- FP11!0nykd
- Cost FREE
#3 – Install and Use anti-virus Software
- Anti-Virus software
- Usually includes anti-virus, antispyware and a personal firewall
- Checks the hard drive and memory for existing infections
- Monitors communications for infected files and web pages
- Updates automatically via the Internet
- Cost: Often FREE from Internet Service Provider
#2 – Apply Patches
- Update software patches:
- Address newly identified vulnerabilities
- Released
- Regularly (Microsoft “Patch Tuesdays”)
- As needed when critical vulnerabilities appear
- Can be downloaded and installed automatically
- Cost: FREE
#1 – Install a Firewall
- Consumer-grade firewalls:
- Available since the late 1990s
- Require little or no configuration
- Available from most large retailers
- Cost: Less than $100
| Chase Paymentech | www.chasepaymentech.com |
| – Cardholder Data Security | www.chasepaymentech.com/datasecurity |
|
|
|
| PCI Security Standards Council | |
| – Validated Payment Applications | www.pcisecuritystandards.org/security_standards/vpa |
| – PTS Certified devices | www.pcisecuritystandards.org/security_standards/ped/pedapprovallist.html |
| – Self-Assessment Questionnaires | www.pcisecuritystandards.org/saq/index.shtml |
| – Prioritized Approach | www.pcisecuritystandards.org/education/prioritized.shtml |
|
|
|
| Visa Cardholder Info Security Program | usa.visa.com/merchants/risk_management/cisp.html |
| – Visa/BBB Data Security Microsite | www.bbb.org/data-security |
| – Visa Alert Page | http://usa.visa.com/merchants/risk_management/cisp_alerts.html |
|
|
|
| MasterCard Site Data Protection Program | https://sdp.mastercardintl.com |
|
|
|
| Trustwave | www.trustwave.com |
| – Portal: Level 4 Merchant Portal | www.trustwave.com/level4pci |
| – Free Risk Profile | http://chasepaymentech.riskprofiler.net referral code: WELCOMECHASEPAY |